Though governments around the world have made an effort to establish national cybersecurity strategies, 66 percent of cybersecurity professionals said that those strategies were incoherent or incomplete, according to a survey conducted by the Enterprise Strategy Group and Information Systems Security Association. […]
ZeroPoint Dynamics, a start-up company specializing in technology that can detect exploit payloads in email and Web content, will be commercialized through the Department of Homeland Security Cyber Security Division’s Transition to Practice program. […]
An old technology is exposing health care, critical infrastructure, and other industries to new cybersecurity problems, as a recent Trend Micro survey finds that pagers can cause vulnerable points for hackers to extract personal information. […]
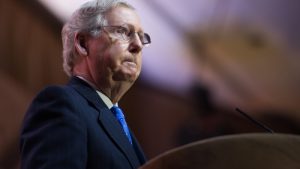
Senate Majority Leader Mitch McConnell, R-Ky., opened a news conference on Monday saying that recent allegations of Russia’s interference in the presidential election as well as the White House’s announcement of additional election cybersecurity investigations should be treated in a bipartisan manner. […]
The White House has ordered a “full review” of hacks related to the most recent presidential election, according to Lisa Monaco, President Obama’s adviser for counterterrorism and homeland security. […]
The state of Georgia said it found evidence of an attempted hack on its voter registration database by a Department of Homeland Security device. […]
President-elect Donald Trump should appoint an ambassador for cybersecurity within his first 180 days in office, according to the President’s Commission on Enhancing National Cybersecurity. […]
An effort to block or delay changes to Rule 41 of the Federal Rules of Criminal Procedure failed to pass the Senate floor, causing the changes to the rule to go into effect on Dec. 1. The changes will allow law enforcement to obtain warrants to search computers in an unknown location and to search any device that the hacker has broken into, potentially granting access to multiple privately owned computers with one warrant. […]
Members of the Senate Intelligence Committee sent a letter to President Obama on Wednesday asking that he declassify information about Russia’s reported attempts to influence the U.S. presidential election. […]
The Department of Homeland Security’s Office of Cybersecurity and Communications announced it had awarded CSRA a contract for $52 million on Nov. 21. […]
President-elect Donald Trump during his transition is relying on two American Enterprise Institute contributors for advice on technology policy, which consists of calls for deregulation of the National Security Agency and an end to net neutrality. […]
The National Initiative for Cybersecurity Education program divided $1 million in grant funding evenly among five academic institutions to support cybersecurity education among students. […]
Rep. Gerry Connolly, D-Va., spearheaded a letter signed by 15 members of the House Foreign Affairs Committee to request that the committee hold a hearing on the attempts by foreign powers to influence the U.S. presidential election. […]
The Department of Defense announced two initiatives based on the past success of Hack the Pentagon and aimed at increasing vulnerability reporting opportunities: a Vulnerability Disclosure Policy and Hack the Army. […]
In determining whether agency CIOs have learned their lesson after the 2015 OPM data breach, Rep. Will Hurd, R-Texas, commended NASA CIO Renee Wynn on her “unprecedented” move to refuse an end-user service provider the authority to operate due to a lack of knowledge about the potential risks of that service. […]
Security measures in cloud adoption will be the fastest growing service in which the government invests in 2017, according to Tom Ruff, vice president of Public Sector America’s and Latin American Markets for Akamai Technologies. […]
In the “Wild West” of augmented reality applications, the U.S. government has to balance the concerns of helping to protect consumer privacy and security while also leaving room for companies to freely innovate, according to witnesses at a Senate Energy and Commerce hearing. […]
In light of the recent distributed denial of service attack that prevented access to multiple U.S. websites as well as the increasing cybersecurity threat posed by Internet of Things devices, the Federal government “needs a new agency” to deal with cybersecurity, according to Bruce Schneier of Harvard University. […]
Though many small businesses may think that they are too trivial to be the target of a cyberattack, even the smallest businesses can face cyberattack and can face serious repercussions, according to Pat Toth, supervisory computer scientist in the computer security division at the National Institute of Standards and Technology and author of NIST’s cybersecurity guide “Small Business Information Security: The Fundamentals.” […]
If agencies improve their threat monitoring, correlation, and protection automation, they could save an estimated 27 percent, or $5 billion annually, of their cybersecurity budgets, according to a MeriTalk survey titled Pedal to the Metal: Mitigating New Threats Faster with Rapid Intel and Automation. […]
The day before the election, the White House and other Federal agencies are getting ready to mitigate and strike back if necessary, in the event of a state-sponsored cyberattack against the United States. Ann Barron-DiCamillo, former director of the Department of Homeland Security’s computer emergency readiness team, said the denial-of-service attack against Dyn in October “had all the signs of…a drill.” […]
All 50 states have reached out to the Department of Homeland Security for cybersecurity services, a DHS official said on the day before Election Day. […]
In the wake of October’s Distributed Denial of Service attack that used hundreds of unsecured devices to prevent access to a number of U.S. websites, Reps. Frank Pallone, D-N.J., and Jan Schakowsky, D-Ill., wrote a letter to Federal Trade Commission Chairwoman Edith Ramirez asking that her agency take action to ensure greater security of Internet of Things devices. […]
If government agencies don’t cooperate with both each other and the private sector on threat intelligence, they’ll never be able to keep up with the hackers working against them, according to Cloudera’s director of cybersecurity strategy, Sam Heywood. […]
The National Institute of Standards and Technology announced the release of CyberSeek, an interactive map that shows cybersecurity job availability by both state and locality. […]
In order to ensure the security of IT devices while also reducing the proliferation of “shadow IT” in the government, agencies must work to create “win-win” compromises with device users, according to panelists at Dell EMC World. […]
The hacker group the Shadow Brokers released files Monday alleging to show which foreign governments and organizations were under surveillance by the National Security Agency. The Shadow Brokers directly asked the U.S. government to pay for the remaining files to be returned. […]
In the push to modernize legacy IT systems, agencies should be more strategic about which systems they choose to invest in, according to experts at Dell EMC World. […]
In the wake of recent Dyn attacks that temporarily shut down major websites such as Twitter, Amazon, and PayPal, Sens. Angus King, I-Maine, and Martin Heinrich, D-N.M., sent a letter to President Obama this week to request a strengthening of the U.S. ability to detect and respond to major vulnerabilities. […]
The White House released a proposed guidance on modernizing Federal IT that is open for public comment until Nov. 26. […]